Enabling SMB Signing on Windows Desktops
What is signing SMB ?
SMB signing means that every SMB 3.1.1 message contains a signature generated using session key and AES. The client puts a hash of the entire message into the signature field of the SMB2 header. If anyone changes the message itself later on the wire, the hash won't match and SMB knows that someone tampered with the data. It also confirms to sender and receiver that they are who they say they are, breaking relay attacks. Ideally, you are using Kerberos instead of NTLMv2 so that your session key starts strong; don't connect to shares with IP addresses and don't use CNAME records - Kerberos is here to help!
By default, domain controllers require SMB signing of anyone connecting to them, typically for SYSVOL and NETLOGON to get group policy and those sweet logon scripts. Less well known is that - starting in Windows 10 - UNC Hardening from the client also requires signing when talking to those same two shares and goes further by requiring Kerberos (it technically requires mutual auth, but for Windows, that means Kerberos).
SMB signing first appeared in Windows 2000, NT 4.0, and Windows 98, it's old enough to drink. Signing algorithms have evolved over time: - SMB 2.02 signing was improved with HMAC SHA-256, replacing the old MD5 method from the late 1990s that was in SMB1 (may it burn in Hades for all eternity). - SMB 3.0 added AES-CMAC. - In Windows Server 2022 and Windows 11, we added AES-128-GMAC signing acceleration, so if you're looking for the best performance and protection combo, start planning your upgrades.
Implementation
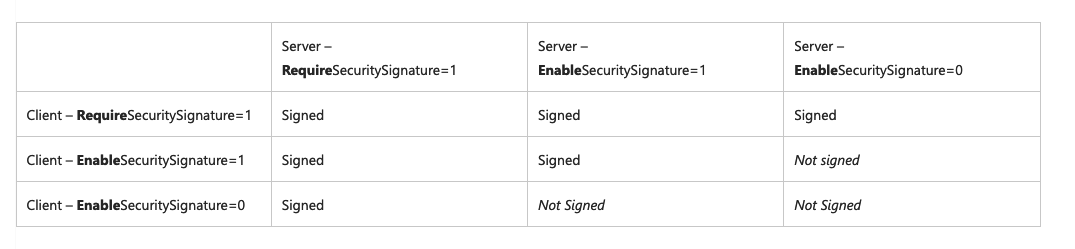
We have four settings to control SMB signing, but they behave and mean things differently with SMB2+ and SMB1.
- Policy: "Microsoft network client: Digitally sign communications (always)"
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\LanManWorkstation\Parameters
RequireSecuritySignature = 1 or 0
- Microsoft network client: Digitally sign communications (if server agrees)
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\LanManWorkstation\Parameters
EnableSecuritySignature = 1 or 0
- Microsoft network server: Digitally sign communications (always)
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters
RequireSecuritySignature = 1 or 0
- Microsoft network server: Digitally sign communications (if client agrees)
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\LanManServer\Parameters
EnableSecuritySignature = 1 or 0
Note my use of bold. "Always" means "required." "If agrees" means "enabled."
These settings live here in the classic Security Settings of computer group policy you'll see by launching GPMC.MSC or GEPEDIT.MSC.
Ressources:
https://techcommunity.microsoft.com/t5/storage-at-microsoft/configure-smb-signing-with-confidence/ba-p/2418102
https://docs.microsoft.com/archive/blogs/openspecification/smb-2-and-smb-3-security-in-windows-10-the-anatomy-of-signing-and-cryptographic-keys